Dickimaw Books Blog 
Ebook Sale July 2025 🔗

The following Dickimaw ebooks are included in the sale:
100% off (free!) short story noir crime fiction I’ve Heard the Mermaid Sing
![]() It’s 1928 and Albert Sternheimer, a yegg (jewel thief) from St Louis, is travelling on the RMS Aquitania with a case of stolen jewels, but unknown to him there’s someone else on board with an interest in him and the contents of his case.
It’s 1928 and Albert Sternheimer, a yegg (jewel thief) from St Louis, is travelling on the RMS Aquitania with a case of stolen jewels, but unknown to him there’s someone else on board with an interest in him and the contents of his case.
100% off (free!) short story cybercrime fiction Unsocial Media
![]() A cybercrime short story cautionary tale about the dangers of sharing too much information. Greg has unwisely accepted a friend request from “Natalie”, a stranger who starts to stalk him after failing to hook him in a scam. The stalking moves from the digital world to real life when Natalie shares a photo of Greg with his neighbour Susie, in what looks like a compromising position. Unknown to any of them, Greg’s wife (the unnamed narrator) has a secret life of her own and is doggedly following Natalie’s trail.
A cybercrime short story cautionary tale about the dangers of sharing too much information. Greg has unwisely accepted a friend request from “Natalie”, a stranger who starts to stalk him after failing to hook him in a scam. The stalking moves from the digital world to real life when Natalie shares a photo of Greg with his neighbour Susie, in what looks like a compromising position. Unknown to any of them, Greg’s wife (the unnamed narrator) has a secret life of her own and is doggedly following Natalie’s trail.
100% off (free!) short story crime fiction Smile for the Camera
![]() Evelyn, a CCTV operator, sees too much information while she monitors a store’s self-service checkout tills in this cybercrime short story about identity theft.
Evelyn, a CCTV operator, sees too much information while she monitors a store’s self-service checkout tills in this cybercrime short story about identity theft.
100% off (free!) short story crime fiction The Briefcase
![]() Convinced that his secretive wife, Annie, is cheating on him, Aide meets an attractive young goth at the pub who helps him pick the lock of Annie's briefcase to search for incriminating evidence.
Convinced that his secretive wife, Annie, is cheating on him, Aide meets an attractive young goth at the pub who helps him pick the lock of Annie's briefcase to search for incriminating evidence.
50% off crime fiction novel The Private Enemy
![]() In the Fenland area of Norfolk, the last Earl of Wynherne is found dead on the study floor of his Gothic mansion. His daughter is missing, having run off after stabbing the seemingly respectable Mr Allerton in the leg. Detective Inspector Charles Hadley and his partner Detective Sergeant Sarah Fenning are called in to investigate, but in this retro world of gangsters and corrupt city police a wrong move could destroy the fragile alliances and trigger war after thirty years of uneasy peace.
In the Fenland area of Norfolk, the last Earl of Wynherne is found dead on the study floor of his Gothic mansion. His daughter is missing, having run off after stabbing the seemingly respectable Mr Allerton in the leg. Detective Inspector Charles Hadley and his partner Detective Sergeant Sarah Fenning are called in to investigate, but in this retro world of gangsters and corrupt city police a wrong move could destroy the fragile alliances and trigger war after thirty years of uneasy peace.
50% off illustrated children’s story The Foolish Hedgehog
![]() A little hedgehog promises his grandmother that he won’t go onto the wasteland (the road) where the dragons (vehicles) live, but one day he’s tempted onto the road by a hungry crow. Will he manage to get home safely? This story can be used to introduce young children to the concepts of road safety and stranger-danger.
A little hedgehog promises his grandmother that he won’t go onto the wasteland (the road) where the dragons (vehicles) live, but one day he’s tempted onto the road by a hungry crow. Will he manage to get home safely? This story can be used to introduce young children to the concepts of road safety and stranger-danger.
Previous Post
 If you have read my short story Smile for the Camera, did you notice that the ending could have two possible interpretations? (No spoilers please!) As a writer, it’s always difficult to tell if something is too obvious or too obscure. If you need a hint, consider the naming scheme and remember that not everyone is what they say or imply that they are.
If you have read my short story Smile for the Camera, did you notice that the ending could have two possible interpretations? (No spoilers please!) As a writer, it’s always difficult to tell if something is too obvious or too obscure. If you need a hint, consider the naming scheme and remember that not everyone is what they say or imply that they are.Recent Posts
 The DRM-free ebook retailer SmashWords has its annual Summer/Winter sale from 1st – 31st July 2025. My crime novel “The Private Enemy” and children’s illustrated story “The Foolish Hedgehog” both have a 50% discount, and my crime fiction short stories “I’ve Heard the Mermaid Sing”, “Unsocial Media”, “Smile for the Camera”, and “The Briefcase” have a 100% discount (i.e. free!) for the duration of the sale. Did you know that you can gift ebooks on SmashWords?
The DRM-free ebook retailer SmashWords has its annual Summer/Winter sale from 1st – 31st July 2025. My crime novel “The Private Enemy” and children’s illustrated story “The Foolish Hedgehog” both have a 50% discount, and my crime fiction short stories “I’ve Heard the Mermaid Sing”, “Unsocial Media”, “Smile for the Camera”, and “The Briefcase” have a 100% discount (i.e. free!) for the duration of the sale. Did you know that you can gift ebooks on SmashWords? If you have read my short story Smile for the Camera, did you notice that the ending could have two possible interpretations? (No spoilers please!) As a writer, it’s always difficult to tell if something is too obvious or too obscure. If you need a hint, consider the naming scheme and remember that not everyone is what they say or imply that they are.
If you have read my short story Smile for the Camera, did you notice that the ending could have two possible interpretations? (No spoilers please!) As a writer, it’s always difficult to tell if something is too obvious or too obscure. If you need a hint, consider the naming scheme and remember that not everyone is what they say or imply that they are. The Ex-Cathedra writing group were delighted to present a cheque for £1,400 to St Martins Housing Trust during their collection at Tesco Harford Bridge on 6th December 2024. The money was raised from sales of the book Tales for Our Times, an anthology of short stories written by the group. The cheque was received by Ian Hanwell on behalf of St Martins. Many thanks to the support of everyone who purchased a copy and to the staff at Tesco Harford Bridge for allowing us to make the presentation there.
The Ex-Cathedra writing group were delighted to present a cheque for £1,400 to St Martins Housing Trust during their collection at Tesco Harford Bridge on 6th December 2024. The money was raised from sales of the book Tales for Our Times, an anthology of short stories written by the group. The cheque was received by Ian Hanwell on behalf of St Martins. Many thanks to the support of everyone who purchased a copy and to the staff at Tesco Harford Bridge for allowing us to make the presentation there. 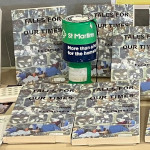 The book launch for the anthology Tales for Our Times, written by Norfolk writing group Ex-Cathedra and published by Smokehouse Press, took place in the Norfolk and Norwich Millennium Library at noon on World Homeless Day (10th October 2024). All profits from the sale of this book will be used to help raise funds to support Norwich-based St Martins Housing Trust in their work to help the homeless into independent living. The book launch included a talk from Dr Jan Sheldon, SEO of St Martins, two readings by authors of the book, and a presentation to the library.
The book launch for the anthology Tales for Our Times, written by Norfolk writing group Ex-Cathedra and published by Smokehouse Press, took place in the Norfolk and Norwich Millennium Library at noon on World Homeless Day (10th October 2024). All profits from the sale of this book will be used to help raise funds to support Norwich-based St Martins Housing Trust in their work to help the homeless into independent living. The book launch included a talk from Dr Jan Sheldon, SEO of St Martins, two readings by authors of the book, and a presentation to the library. Tales for Our Times is an anthology of forty stories featuring loss and hope, dreams of love and belonging, biography and science fiction and adventure. Written by Norfolk-based writing group Ex-Cathedra and published by Smokehouse Press, the book will be launched on World Homeless Day 10th October 2024 midday at the Norwich and Norfolk Millennium Library. All profits from the sale of this book will be used to help raise funds to support Norwich-based St Martins Housing Trust in their work to help the homeless into independent living.
Tales for Our Times is an anthology of forty stories featuring loss and hope, dreams of love and belonging, biography and science fiction and adventure. Written by Norfolk-based writing group Ex-Cathedra and published by Smokehouse Press, the book will be launched on World Homeless Day 10th October 2024 midday at the Norwich and Norfolk Millennium Library. All profits from the sale of this book will be used to help raise funds to support Norwich-based St Martins Housing Trust in their work to help the homeless into independent living.Search Blog
📂 Categories
- Autism
- Books
- Children’s Illustrated Fiction
- Illustrated fiction for young children: The Foolish Hedgehog and Quack, Quack, Quack. Give My Hat Back!
- Creative Writing
- The art of writing fiction, inspiration and themes.
- Crime Fiction
- The crime fiction category covers the crime novels The Private Enemy and The Fourth Protectorate and also the crime short stories I’ve Heard the Mermaid Sing and I’ve Heard the Mermaid Sing.
- Fiction
- Fiction books and other stories.
- Language
- Natural languages including regional dialects.
- (La)TeX
- The TeX typesetting system in general or the LaTeX format in particular.
- Music
- Norfolk
- This category is about the county of Norfolk in East Anglia (the eastern bulgy bit of England). It’s where The Private Enemy is set and is also where the author lives.
- RISC OS
- An operating system created by Acorn Computers in the late 1980s and 1990s.
- Security
- Site
- Information about the Dickimaw Books site.
- Speculative Fiction
- The speculative fiction category includes the novel The Private Enemy (set in the future), the alternative history novel The Fourth Protectorate, and the fantasy novel Muirgealia.
🔖 Tags
- Account
- Alternative History
- Sub-genre of speculative fiction, alternative history is “what if?” fiction.
- book samples
- Bots
- Conservation of Detail
- A part of the creative writing process, conservation of detail essentially means that only significant information should be added to a work of fiction.
- Cookies
- Information about the site cookies.
- Dialect
- Regional dialects, in particular the Norfolk dialect.
- Docker
- Education
- The education system.
- Ex-Cathedra
- A Norfolk-based writing group.
- Fantasy
- Sub-genre of speculative fiction involving magical elements.
- File formats
- Hippochette
- A pochette (pocket violin) with a hippo headpiece.
- History
- I’ve Heard the Mermaid Sing
- A crime fiction short story (available as an ebook) set in the late 1920s on the RMS Aquitania. See the story’s main page for further details.
- Inspirations
- The little things that inspired the author’s stories.
- Linux
- Migration
- Posts about the website migration.
- Muirgealia
- A fantasy novel. See the book’s main page for further details.
- News
- Notifications
- Online Store
- Posts about the Dickimaw Books store.
- Quack, Quack, Quack. Give My Hat Back!
- Information about the illustrated children’s book. See the book’s main page for further details.
- Re-published
- Articles that were previously published elsewhere and reproduced on this blog in order to collect them all together in one place.
- Sale
- Posts about sales that are running or are pending at the time of the post.
- Site settings
- Information about the site settings.
- Smile for the Camera
- A cybercrime short story about CCTV operator monitoring a store’s self-service tills who sees too much information.
- Story creation
- The process of creating stories.
- TeX Live
- The Briefcase
- A crime fiction short story (available as an ebook). See the story’s main page for further details.
- The Foolish Hedgehog
- Information about the illustrated children’s book. See the book’s main page for further details.
- The Fourth Protectorate
- Alternative history novel set in 1980s/90s London. See the book’s main page for further details.
- The Private Enemy
- A crime/speculative fiction novel set in a future Norfolk run by gangsters. See the book’s main page for further details.
- Unsocial Media
- A cybercrime fiction short story (available as an ebook). See the story’s main page for further details.
- World Book Day
- World Book Day (UK and Ireland) is an annual charity event held in the United Kingdom and the Republic of Ireland on the first Thursday in March. It’s a local version of the global UNESCO World Book Day.
- World Homeless Day
- World Homeless Day is marked every year on 10 October to draw attention to the needs of people experiencing homelessness.